The Complete Guide to Storage and Security for High-Value Digital Assets

Losing access to your cryptocurrency or blockchain art collection can happen in seconds. A phishing email, a compromised device, or a forgotten password can wipe out years of investment. The good news? Most losses are preventable when you understand the fundamentals of digital asset security and apply them consistently.
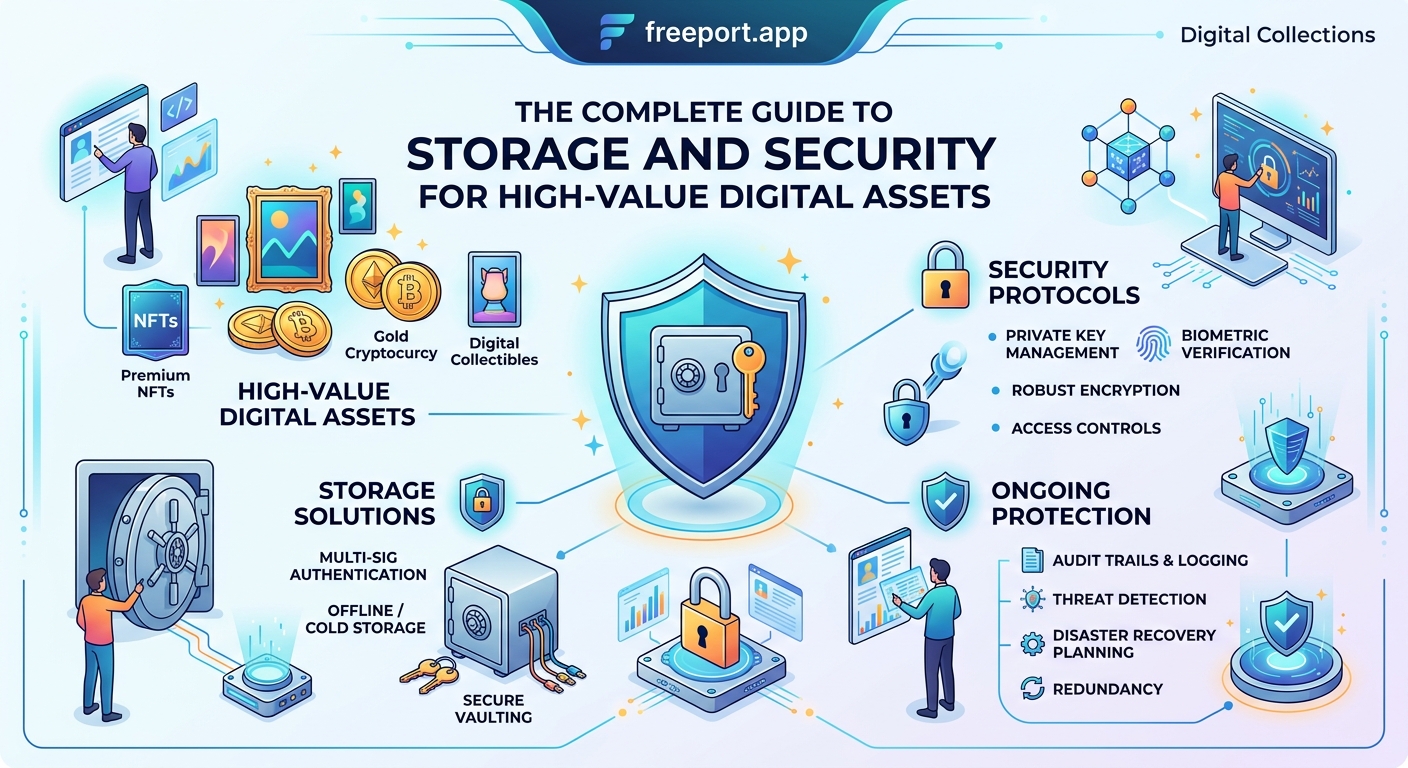
Securing digital assets requires multiple layers of protection including hardware wallets, strong authentication, regular backups, and careful transaction practices. The most effective security strategy combines cold storage for long-term holdings, hot wallets for active use, and rigorous verification habits. Understanding common attack vectors and implementing proven safeguards protects your cryptocurrency and blockchain art from theft, loss, and unauthorized access while maintaining convenient access when needed.
Understanding the security landscape for digital holdings
Digital assets exist in a fundamentally different environment than traditional property. Your cryptocurrency and blockchain art are secured by cryptographic keys rather than physical vaults or legal documents. This creates unique vulnerabilities.
When you own digital assets, you control private keys that prove ownership. Anyone with access to these keys controls your assets. No bank will reverse fraudulent transactions. No insurance policy covers most losses. No password reset email can restore access if you lose your recovery phrase.
The blockchain itself is highly secure. The weak points are almost always human error, device compromise, or social engineering. Attackers target your devices, trick you into revealing credentials, or exploit poor security practices.
Understanding this threat model changes how you approach protection. You need defenses against both technical attacks and psychological manipulation.
Cold storage versus hot wallet strategies
The foundation of digital asset security is separating your holdings based on access needs.
Cold storage keeps private keys completely offline. Hardware wallets, paper wallets, and air-gapped devices fall into this category. These solutions protect against remote attacks because there’s no internet connection to exploit.
Hot wallets maintain internet connectivity for convenience. Mobile apps, browser extensions, and exchange accounts allow instant transactions but expose you to online threats.
Most collectors use a hybrid approach. Store 80-90% of holdings in cold storage. Keep only what you need for active trading or regular transactions in hot wallets.
This strategy limits your exposure. If a hot wallet is compromised, you lose only a small portion of your portfolio. Your core holdings remain protected offline.
| Storage Method | Security Level | Convenience | Best For |
|---|---|---|---|
| Hardware wallet | Very high | Medium | Long-term holdings |
| Paper wallet | High | Low | Inheritance planning |
| Mobile wallet | Medium | High | Daily transactions |
| Exchange account | Low to medium | Very high | Active trading only |
| Multi-signature wallet | Very high | Low | High-value assets |
Setting up hardware wallet protection
Hardware wallets are the gold standard for securing significant digital asset holdings. These physical devices store private keys in isolated environments that never expose them to internet-connected computers.
- Purchase hardware wallets directly from manufacturers, never from third-party sellers or marketplaces where devices could be tampered with.
- Verify the device is genuine using the manufacturer’s authentication process when you receive it.
- Initialize the device in a private location without cameras or other people present.
- Write down your recovery phrase on the provided card using pen, never typing it into any digital device.
- Store recovery phrases in multiple secure physical locations, such as a home safe and bank safety deposit box.
- Test the recovery process with a small amount before transferring significant holdings.
- Enable PIN protection and consider using a passphrase for additional security layers.
The recovery phrase is the master key to your assets. Anyone who obtains it controls everything in that wallet. Never photograph it, never store it digitally, and never enter it into any website or application claiming to “verify” or “sync” your wallet.
When transferring assets to your hardware wallet, start with a test transaction. Send a small amount first, verify it arrives correctly, then proceed with larger transfers. This practice catches address errors before they become expensive mistakes.
Authentication and access control essentials

Strong authentication prevents unauthorized access even if someone obtains your device or account credentials.
Enable two-factor authentication on every service that supports it. Use authenticator apps rather than SMS when possible. Text messages can be intercepted through SIM swapping attacks where criminals convince your phone carrier to transfer your number to their device.
For exchange accounts and wallet services, consider these practices:
- Use unique, complex passwords for each service
- Store passwords in an encrypted password manager
- Enable withdrawal address whitelisting when available
- Set up email alerts for all account activity
- Use biometric authentication on mobile devices
- Regularly review connected devices and active sessions
Create separate email addresses for different security tiers. Use one email exclusively for high-value accounts, another for general crypto services, and a third for newsletters and low-security signups. This compartmentalization limits the damage if one email account is compromised.
The strongest security measure is the one you’ll actually use consistently. A moderately secure system you follow every time beats a theoretically perfect system you only apply occasionally.
Protecting against phishing and social engineering
Technical security measures mean nothing if you’re tricked into voluntarily giving away access. Phishing attacks targeting crypto holders have become increasingly sophisticated.
Common attack patterns include:
- Fake emails from exchanges or wallet providers requesting urgent action
- Discord or Telegram messages offering exclusive investment opportunities
- Websites that look identical to legitimate platforms but capture your credentials
- Tech support scammers claiming to help recover lost funds
- Fake airdrops or giveaways requiring you to connect your wallet
Develop verification habits before taking any action. Bookmark official websites and only access them through your bookmarks, never through email links. Check URLs carefully for subtle misspellings. Verify social media accounts have official verification badges.
No legitimate service will ever ask for your recovery phrase or private keys. This is the crypto equivalent of a bank asking for your PIN. Anyone requesting this information is attempting theft.
When someone offers an investment opportunity that seems too good to be true, it almost certainly is. High-pressure tactics, guaranteed returns, and urgency are red flags. Take time to research independently before committing funds.
Transaction verification and address management
Sending cryptocurrency to the wrong address means permanent loss. The blockchain cannot reverse transactions or recover funds sent to incorrect destinations.
Before confirming any transaction:
- Verify the complete receiving address character by character, not just the first and last few characters.
- Use address book features to save verified addresses for frequent recipients.
- Send a small test transaction first when using a new address.
- Double-check the amount and network to prevent sending assets on the wrong blockchain.
- Review transaction fees to avoid overpaying during network congestion.
Clipboard malware is a real threat. Some malicious software monitors your clipboard and replaces copied cryptocurrency addresses with attacker-controlled addresses. Always verify the pasted address matches what you copied.
For blockchain art and NFT transactions, confirm you’re interacting with authentic smart contracts. Scammers create fake versions of popular collections and marketplaces. Check contract addresses against official sources before approving transactions.
When building a valuable digital art collection, understanding how to authenticate digital art becomes crucial for both artistic value and security purposes.
Backup strategies that actually work
Backups protect against device failure, loss, or damage. But poorly executed backups create new vulnerabilities.
Your recovery phrase backup strategy should include:
- Multiple physical copies stored in different secure locations
- Fireproof and waterproof storage containers
- Clear instructions for heirs or trusted individuals
- Regular verification that backups remain accessible and legible
- No digital copies on computers, phones, or cloud storage
Consider using metal backup plates designed for recovery phrases. These resist fire, water, and physical damage better than paper. Several companies make stamping or engraving systems specifically for this purpose.
For complex portfolios with multiple wallets, maintain an encrypted inventory document listing what assets exist where. Store this separately from your actual keys. It helps you or your heirs understand the full scope of holdings without providing access.
Test your backup recovery process periodically. Set up a new device using your backup materials to confirm everything works. This practice reveals problems while you can still fix them.
Multi-signature wallets for high-value holdings
Multi-signature (multisig) wallets require multiple private keys to authorize transactions. This creates security through distributed control.
A 2-of-3 multisig wallet, for example, generates three keys but only requires two to move funds. You might keep one key on a hardware wallet, one in a safe deposit box, and give one to a trusted family member. An attacker would need to compromise two separate locations to steal your assets.
Multisig provides several advantages:
- Protection against single point of failure
- Shared control for business or family assets
- Inheritance planning with built-in executor access
- Defense against coercion or threats
The tradeoff is increased complexity. Setting up and using multisig wallets requires more technical knowledge. Transaction processes take longer. But for significant holdings, this additional friction provides valuable security.
Several wallet providers offer user-friendly multisig solutions. Research options that match your technical comfort level and security requirements.
Smart contract interactions and wallet permissions
When you connect your wallet to decentralized applications or marketplaces, you grant permissions that can be exploited if you’re not careful.
Some smart contract approvals allow unlimited access to specific tokens in your wallet. Malicious contracts can drain approved tokens even after your initial interaction. This is particularly relevant for collectors engaging with NFT marketplaces and DeFi platforms.
Before approving any smart contract interaction:
- Research the project and verify you’re using the official contract
- Review exactly what permissions you’re granting
- Use wallet security features that clearly display approval details
- Revoke unnecessary approvals periodically using tools designed for this purpose
- Consider using a separate wallet for experimental or higher-risk interactions
Understanding how smart contracts are revolutionizing art ownership helps you appreciate both their power and potential risks when improperly secured.
Network and device security fundamentals
Your digital asset security is only as strong as the devices you use to access them.
Maintain updated operating systems and applications. Security patches address known vulnerabilities that attackers actively exploit. Enable automatic updates when possible.
Use dedicated devices for high-value transactions when feasible. An old smartphone or tablet used exclusively for crypto activities reduces exposure to malware from other activities.
Avoid public WiFi networks for any crypto-related activities. If you must use public networks, connect through a reputable VPN service first. Better yet, use mobile data instead.
Keep your devices physically secure. Enable full-disk encryption. Use strong lock screen protections. Consider what happens if your phone is stolen while unlocked.
Install security software from reputable vendors. While no antivirus is perfect, quality security tools catch many common threats before they compromise your system.
Estate planning and inheritance considerations
Digital assets present unique challenges for inheritance. Without proper planning, your holdings could become permanently inaccessible when you die.
Create clear instructions for heirs that explain:
- What digital assets you own and where they’re stored
- How to access recovery phrases and hardware wallets
- Basic procedures for moving or selling assets
- Trusted contacts who can provide technical assistance
- Tax implications and reporting requirements
Store these instructions separately from your actual keys. You want heirs to know what exists and how to access it, but not have immediate access that could be exploited while you’re alive.
Some hardware wallet manufacturers offer inheritance planning services. Multisig wallets provide built-in solutions where trusted individuals hold keys that become active according to predetermined conditions.
Consult with estate planning attorneys familiar with digital assets. Laws and best practices continue to evolve in this area.
Staying current with evolving threats
The security landscape changes constantly. Attack methods that didn’t exist last year become common this year. Staying informed helps you adapt your practices.
Follow security researchers and organizations focused on cryptocurrency protection. Many share information about emerging threats and vulnerabilities.
Participate in communities of collectors and investors who discuss security practices. Learning from others’ experiences helps you avoid similar mistakes.
When you hear about major hacks or exploits, understand what happened and whether your practices leave you vulnerable to similar attacks. Each incident provides lessons you can apply to your own security.
Be skeptical of new platforms, services, and investment opportunities. Let others test them first. The potential upside of being an early adopter rarely justifies the security risks.
Review and update your security practices annually. What worked last year might need adjustment based on new threats, changed circumstances, or expanded holdings.
Common mistakes that compromise security
Even experienced holders make errors that create vulnerabilities. Recognizing these patterns helps you avoid them.
Reusing passwords across services means one breach compromises multiple accounts. Use unique passwords everywhere, managed through encrypted password managers.
Storing recovery phrases digitally seems convenient but creates massive risk. Screenshots, photos, and text files are vulnerable to device compromise, cloud breaches, and accidental sharing.
Trusting custodial services with all your holdings concentrates risk. Exchanges can be hacked, freeze accounts, or even collapse. Maintain control of significant assets in self-custody solutions.
Ignoring small security warnings often precedes larger problems. That slightly suspicious email, unusual login notification, or unexpected permission request deserves investigation.
Rushing transactions leads to mistakes. Take time to verify details. The few extra seconds of careful review prevent irreversible errors.
Understanding red flags every digital collector should watch for extends beyond purchasing decisions to security practices as well.
Building security habits that stick
Knowledge means nothing without consistent application. The goal is making security practices automatic rather than occasional.
Start with the highest-impact measures first. Getting your main holdings into hardware wallet cold storage provides immediate risk reduction. You can refine other practices over time.
Create checklists for common activities. A transaction verification checklist ensures you complete all steps every time. An account setup checklist guarantees you enable proper security features.
Schedule regular security reviews. Monthly, quarterly, or annually, depending on your activity level, review your practices, update software, check backup accessibility, and revoke unnecessary permissions.
Treat security as an ongoing practice rather than a one-time setup. Your circumstances change, your holdings grow, and new threats emerge. Adapt accordingly.
When considering what happens to your blockchain art when platforms shut down, proper security practices ensure you maintain access regardless of platform changes.
Making security work for your situation
There’s no universal perfect security setup. The right approach depends on your holdings, technical comfort, risk tolerance, and usage patterns.
Someone holding $500 in cryptocurrency needs different security than someone with a six-figure portfolio. Active traders have different requirements than long-term holders. Technical experts can implement solutions that would frustrate less technical users.
Assess your specific situation honestly. What are your actual risks? What security measures will you realistically maintain? Where do convenience and security need to balance?
Start with fundamentals that apply universally. Hardware wallet cold storage for significant holdings. Strong unique passwords. Two-factor authentication. Careful transaction verification. Build from this foundation based on your needs.
Accept that perfect security is impossible. The goal is managing risk to acceptable levels while maintaining usable access to your assets. Finding this balance requires ongoing adjustment as your situation evolves.
Your digital assets represent real value that deserves real protection. The time invested in proper security practices pays dividends through peace of mind and actual preservation of your holdings. Start with one improvement today, then build from there.





